In order to successfully use PDQ Deploy and PDQ Inventory, the console and target computers must have the following firewall ports / services enabled:
•Windows Firewall: Allow inbound file and printer sharing exception
This rule allows the IPC$ and ADMIN$ shares to be available. Administrative access to these shares is required.
•Windows Firewall: Allow ICMP exceptions - (Allow inbound echo request)
This rule allows a target computer to respond to ping requests. Ping is used by PDQ Inventory to determine the online status of a computer. Keep in mind that PDQ products ping the FQDN (Fully Qualified Domain Name) of a computer to determine if it is online and available.
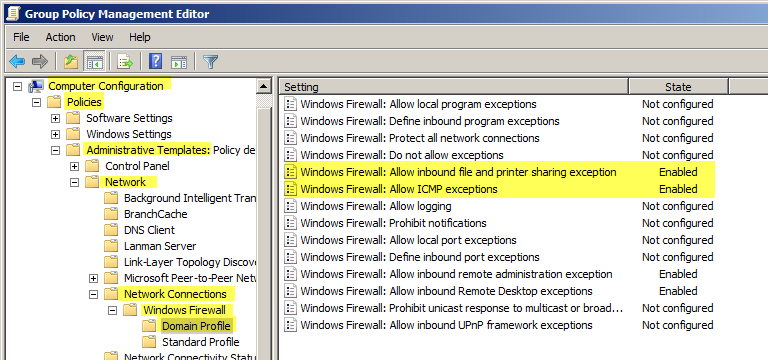
If you enable these rules via Group Policy (GPO) (recommended) you should use the following path:
Computer Configuration\Policies\Administrative Templates\Network\Network Connections\Windows Firewall\Domain Profile
If you enable these rules on computers that are not members of an Active Directory (AD) domain then use the following path:
Computer Configuration\Policies\Administrative Templates\Network\Network Connections\Windows Firewall\Standard Profile
If the target computer is not a member of an Active Directory domain then you may need to enable Remote UAC. When Remote UAC is enabled local administrative accounts are prohibited from accessing system shares such as ADMIN$. This can be a huge problem if you need to manage remote systems with a local account. For more information, see Access Denied-Failure to connect to ADMIN$ share Error.
PDQ products use Server Message Block (SMB) to communicate with target computers. If you can manage remote computers using standard Windows' administration tools you should be set as far as ports go. The following ports are used by SMB:
•UDP 137
•UDP 138
•UDP 445
•TCP 139
•TCP 445
© 2018 PDQ.com Corporation. All rights reserved.
PDQ.com is a trademark of PDQ.com Corporation. All other product and company names are the property of their respective owners.
Help Version: 17.1.0.0